Main Content
Stratus Concept
Rightsized Technology
This book will help your business stay safe. Follow this link to Amazon:
Cyber Security - Hosting - Phones - Email - Productivity Tools - Backup
Transforming Technologies for Your Business
What does your Business Need?

|
Find out what solutions are available for your business: |
AI generated comparison of Microsoft 365 and Google Workspace
Concerned about cyber insurance?
Request a technology and cybersecurity assessment for your business today!
Schedule One NowHow safe is your identity? Are you sure?
Account details stolen during data breaches can lead to identity theft years after the breach.
Search for breachesIs your Cyber Security Plan documented?
Many businesses are required to have a Written Information Security Plan.
Request your custom WISPDo you need reliable web hosting?
Both developers and visitors will appreciate you having high quality hosting!
Get great web hostingSecurity
The cybersecurity threat landscape is rapidly evolving and expanding. Businesses should use layered protection. This includes endpoints to networks to the cloud and the people.
Staff Training
Core training includes: Cybersecurity Awareness training, Dark Web search ,Simulated PHISHing, Weekly mini-training, Written policies and procedures.
Also available: HIPAA and Sexual Harassment modules.
Message filtering stops the junk and lets the good email through. Messages containing offensive, harmful, or policy violating content are held for user review, while good messages continue on their way.
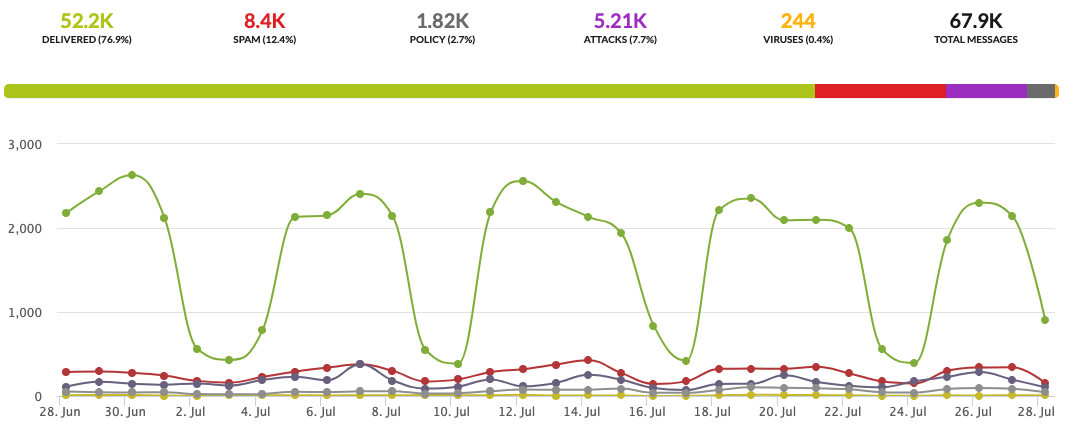
Message filtering helps to keep users safe and gives you confidence that your email infrastructure is shielded from harm.
Network
Big Security in a Small Appliance
Your business needs a small-footprint, cost-effective security appliance that delivers all the features present in higher-end enterprise firewalls, including:
- Virtual Private Nerwork (VPN)
- AI-powered anti-malware
- Threat correlation
- DNS-filtering
Cloud
Security for your SaaS
As much of your business data is in cloud-based services, it is imperitive that it is backed up and not corrupted.
Computers
The key components for protecting Computers and servers are end-point malware detection and recovery protection (EPP) and appropriate backup & disater recovery (BDR) for Windows, Mac, and Linux.
EPP provides these features:
- Prevention and protection against security threats
- The ability to apply control (allow/block) software, scripts and processes
- The ability to detect and prevent threats using behavioral analysis of device activity, application and user data
- Facilitates investigation of incidents and Provides guidance for remediation
BDR protects:
Physical and virtual servers -- Workstations and documents -- Applications and databasesLearn more about BDR
Communication
Phones
Collaborate from anywhere – On the device of your choice
Cloud-based VoIP
Whether you need a business line with great features or apps to work from anywhere, we make it super simple to get started.
Keep your number or choose a new one at no extra cost.
Dig Deeper
Email is a necessity for most businesses.
Many small businesses start off with whatever their webhost provides or a free email account. As business grows, these services can become hard to manage and dangerous.


Stratus Concept offers the top 2 business-class email services: Microsoft 365 and Google Workspace.
Also, for businesses that handle confidetial information there is integrated secure messageing available.
Website
It Is The 1st Impression You Get to Make
The service and quality provide by web hosts varies greatly.
Your web host should provide: automatic backups and easy retores, SSL certificate, software update, a parallel staging site for validating changes, malware scanning, performance tuned server, Content Delivery Network (CDN)
Productivity
Google Workspace
Familiar tools alow work from anywhere, on any device
Google Workspace includes other familiar tools beyond Gmail and Calendar – get access to business versions of Google Meet, Chat, Drive, Docs, Sheets, and more in a single, easy to manage subscription with automatic updates.
Experience AI with Gemini!

Microsoft 365 Apps
Create, view, and edit in real time across all your devices with desktop and mobile apps for Windows PCs, iOS, Android, and Mac with Microsoft 365 Apps for business
The standard tools for traditional business
Always up-to-date desktop and mobile versions of Office apps: Outlook, Word, Excel, PowerPoint, OneNote.
Web versions of Word, Excel, and PowerPoint.
File storage and sharing with 1 TB of OneDrive cloud storage.
File Sharing
There are many ways to share documents with both internal and external stakeholders.
Is your file sharing safe and secure?
Files sharing tools need to be designed for business use. such as: Egnyte, Axcient sync360, and Dropbox for Business.
Documents
Keeing documents online is more than just not having to store paper. To be able to find the documents you need, they need to be searchable.
Some Foxit Pro + features:- PDF Editing
- Stamping
- Bates Numbering
- Image OCR conversion
- E-Signature
Applications
Sometimes the Out-of-the-Box tools are not exactly what you want or need. Whether you issue is with internal workflow or client interaction, custom development and integration can bring your business to the next level
Website Enhancements
Wordpress is a fabulous website system, and but getting the site to act and display exactly what you want is not alway straight forwad.
API integrations
Cloud-based tools are great and many have linkages to other tools you use, but sometimes you need a connection that is not available or the one you have is not working the ay you want.


